Hybrid IT Security
Security prepared to get the best of the private and public cloud. Having the right strategy, coupled with expert management, can help you get the best of both worlds.
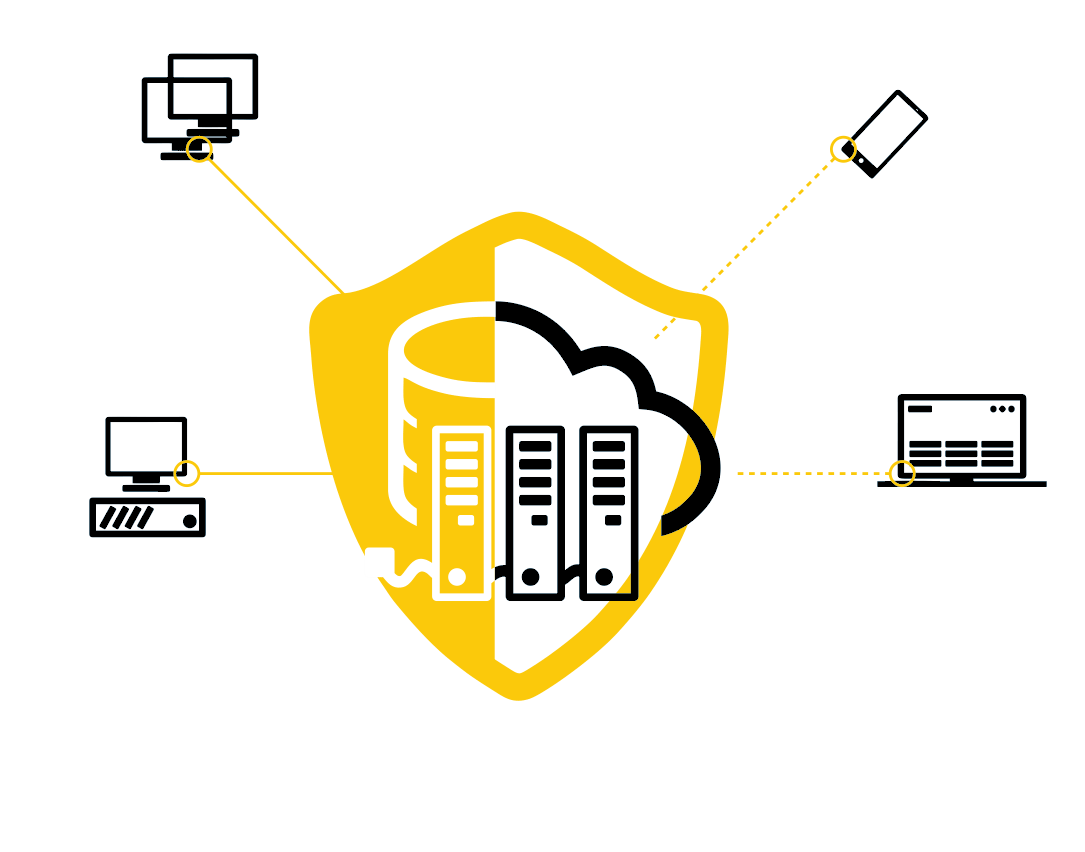
Hybrid infrastructure security
The data center has evolved over the years to an environment composed of physical and virtual infrastructures where cloud computing is more present than ever.
Managing a hybrid environment is complex. The difference in concept between a local environment and the public cloud makes it difficult to see globally and apply security controls.
The added challenge is the added complexity of protecting information as it traverses on-premises, public cloud, and private cloud environments.
OUR VISION
Seamless security
From Velorcios we provide a security model designed to ensure consolidated visibility and security for a hybrid infrastructure.
For the protection of infrastructure and information, Velorcios uses data-centric security techniques in combination with identity-based controls. Using advanced data encryption techniques to protect data at rest and on the move through the private to public cloud, and vice versa, ensures the protection of information. Cloud resource access management adds an additional layer of role-based access rights.
Our objective in the protection of hybrid infrastructures is:
- Protect servers, storage and networks in a hybrid IT model.
- Scale security without falling into a vendor lock-in.
- Reduction of operating costs by consolidating security.
- Integrate security policies in the cloud and on-premises infrastructure to maintain regulatory compliance.
- Provide visibility regardless of location, both on-premises and public cloud.

Hybrid infrastructure security integrates the following:
DRaaS (Disaster Recovery as a service)
BaaS (Backup as a Service)
CASB (Cloud access security broker)
Static and moving data encryption
More information on Hybrid IT security
Our specialization in everything related to the technological options available in the market, together with the knowledge of our clients on the operation of their respective sectors of activity, form the perfect tandem when drawing up the most convenient roadmap in the process of protecting hybrid IT environments.

